Business communication has quietly become the biggest cybersecurity battleground. It’s no longer just about protecting networks or endpoints; attackers are now targeting how teams talk, share, and collaborate. Email, chat tools, and cloud-based platforms are where real business decisions happen, which makes them the most valuable entry points.
In 2026, the shift is clear: attackers don’t need to “hack” systems anymore. They simply log in.
Communication Is the New Attack Surface
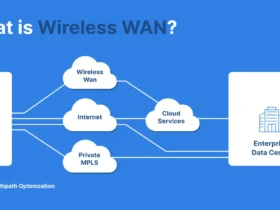
Most modern businesses rely on a mix of email, cloud platforms, and messaging tools. This convenience has created a wide and often fragmented attack surface.
Instead of breaking into systems, attackers now target:
- Email conversations
- Shared documents
- Login credentials
A report by IBM shows that stolen or compromised credentials remain one of the top initial attack vectors in breaches.
This shift means security is no longer just IT’s responsibility—it directly impacts daily business operations.
Email Security Is Being Rebuilt from the Ground Up
Email remains the backbone of business communication and also the most exploited channel. Legacy security layers like basic spam filters are no longer enough.
Organizations are now investing in stronger authentication protocols such as SPF, DKIM, and DMARC, but adoption is still inconsistent. More importantly, businesses are rethinking the entire infrastructure behind their communication systems.
Instead of patching security on top, many are moving toward a business webmail hosting solution that integrates encryption, identity validation, and threat detection directly into the platform. This approach reduces reliance on fragmented tools and creates a more secure communication environment by design.
Remote and Hybrid Work Brings New Risks
Remote and hybrid work models aren’t going anywhere. But they have expanded the attack surface dramatically.
Employees working from home or on mobile devices often use a mix of secure corporate platforms and consumer tools. While this flexibility improves productivity, it also introduces complexity:
- Personal devices may not have the same security configurations.
- Collaboration platforms like Slack or Teams become rich targets for credential theft and covert lateral movement.
- Shared cloud resources can be misconfigured and expose sensitive files or internal discussions.
Even internal voice calls and SMS can be spoofed or weaponized if not properly protected and monitored.
This is why businesses are placing more emphasis on secure communication frameworks that unify security controls across email, messaging, and remote access, instead of treating them as separate silos.
Zero Trust Is Expanding to Communication
The idea of “never trust, always verify” is now being applied directly to communication tools. Every email, attachment, or shared link is treated as potentially unsafe until verified.
This approach reduces internal threats and limits the damage of compromised accounts. A study on Zero Trust implementation shows that applying it to communication systems can drastically reduce lateral movement within networks.
Real‑Time Monitoring and Threat Intelligence Integration
Threats don’t wait, so security controls shouldn’t either.
Legacy defenses often rely on periodic scans or static lists of known threats. But attackers are now combining AI, human insight, and social engineering to craft campaigns that evade traditional detection methods.
That’s where real‑time monitoring, behavior analytics, and threat intelligence feeds come in. These systems don’t just look for “known bad patterns.” They detect deviations from normal patterns, such as unusual login times, odd attachment behaviors, or messages that don’t match typical internal communication styles.
Coupling these insights with external threat intelligence helps teams respond faster and with more context, making it far harder for attackers to hide in plain sight.
7. Resilience – Not Just Prevention, Is the New Goal
Let’s be honest: in 2026, it’s no longer realistic to think any organization can prevent every attack.
That’s why the focus in cybersecurity is now shifting from pure prevention to resilience, the ability to detect attacks quickly, understand their impact, and recover with minimal disruption.
Resilience includes:
- Immutable backups and disaster recovery planning
- Integrated incident response across communication platforms
- Continuous training programs that simulate realistic attack scenarios
Research shows that organizations with strong resilience planning recover from cyber incidents much faster and with lower financial impact than those relying solely on prevention.
The message is simple: “We will be attacked, but we won’t be knocked offline.
The Human Factor Still Matters
Despite all technological advancements, humans remain the weakest link. Most successful attacks still rely on manipulation rather than technical flaws.
Research consistently shows that phishing and social engineering account for a large percentage of breaches. This means employee awareness and behavior monitoring are just as important as technical defenses.
Final Thoughts
As we move into 2026, one thing is clear: business communication is now a frontline in cybersecurity. It’s no longer enough to secure networks or devices. Companies must secure how people interact, share information, and make decisions.
Organizations that invest in secure, intelligent communication systems today will be better prepared for the evolving threat landscape. Those that don’t may find that their biggest vulnerability isn’t their technology, it’s how they use it.